NextDNS for Security and Privacy
One of the most prevalent ways tracking and analytics happens is via various ad and tracking services. You can learn more about how exactly tracking on the web works here. These services are ran by Google, Meta, and a bunch of other for-profit companies that have managed to figure out how to monetize and capitalize on every click, interaction, and view you perform. You can see how affected you personally are with this neat tool by the EFF
Here's my score!
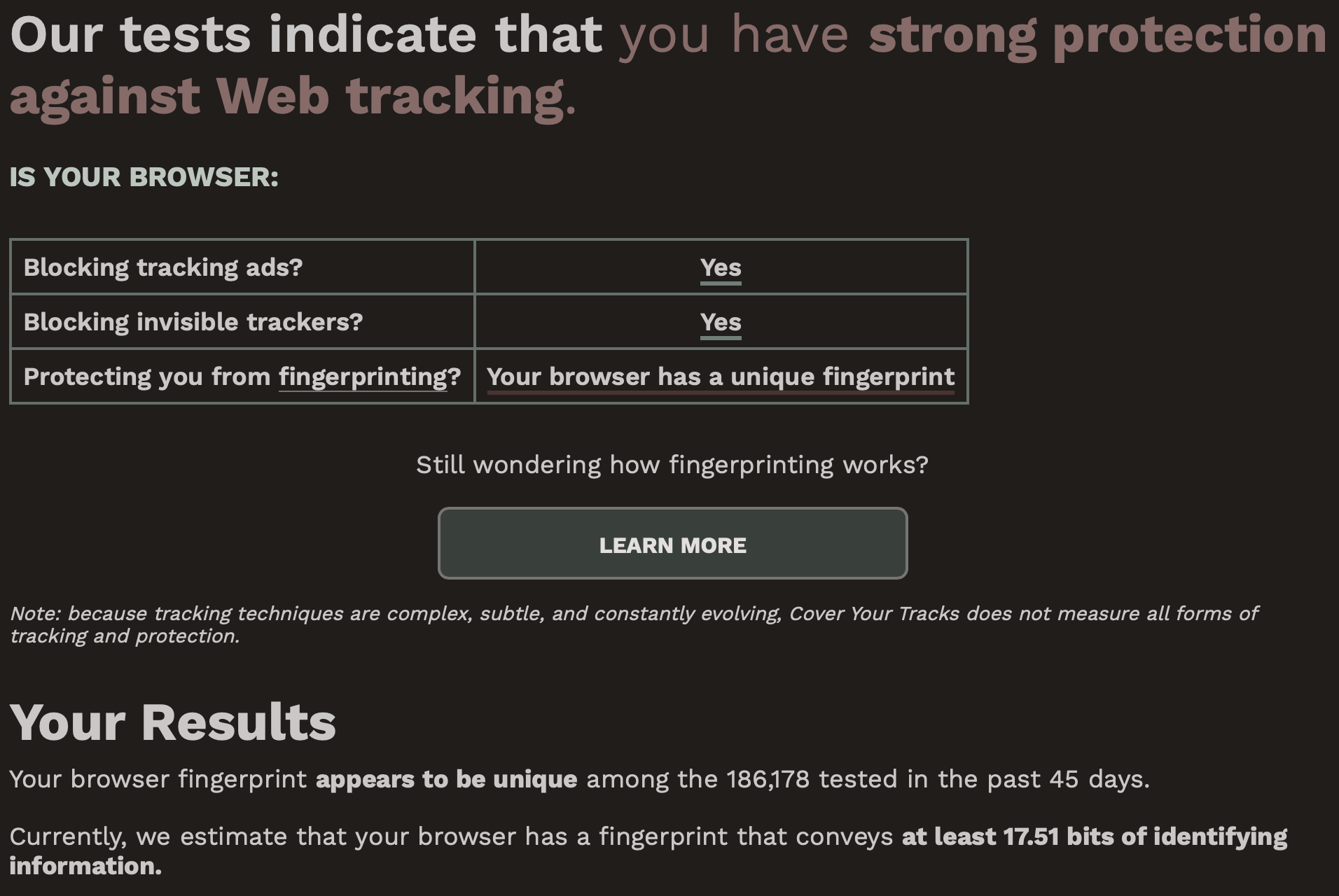
I begin to feel perceived going through all this 😓.
In addition to the nauseating nature of ads and tracking on the internet, there are security ramifications to ads and tracking on the web. Towards the end of 2022, the FBI published a recommendation to use ad blockers for security reasons. This recommendation has since been taken down.
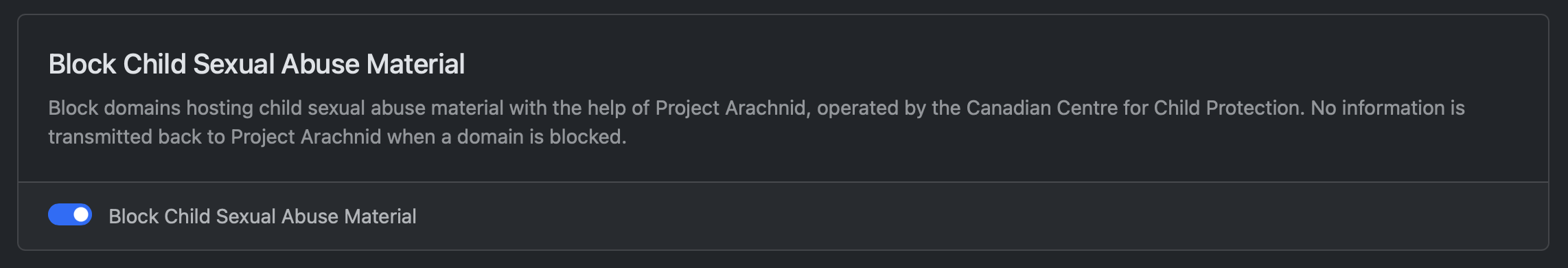
Additionally, it must be noted that DNS level control of a network allows controlling the types of content accessed including preventing devices from accessing known child sexual abuse material, compromised domains, known historic domains related to malware, and more. Large corporations primarily implement similar capabilities through web proxies instead of DNS level filtering. Don't mistake me, corporations do perform DNS level filtering, just not to the extent where it's a primary mechanism for defense. DNS is generally "managed" and "audited" in corporate environments rather than directly controlled.
NextDNS Advantages
NextDNS poses a number of advantages over traditional solutions, like PiHole, for the aforementioned concerns.
- PiHole
PiHole is a DNS server with a web interface that allows setting drop-lists for domain names that should not be resolved. The effect is that entire ad-serving domains can be prevented from loading on end user devices.
The best-selling feature of NextDNS is that it supports all the features you could want right out of the box. Want to block child sexual abuse material (why wouldn't you?)? That's just a toggleable button.
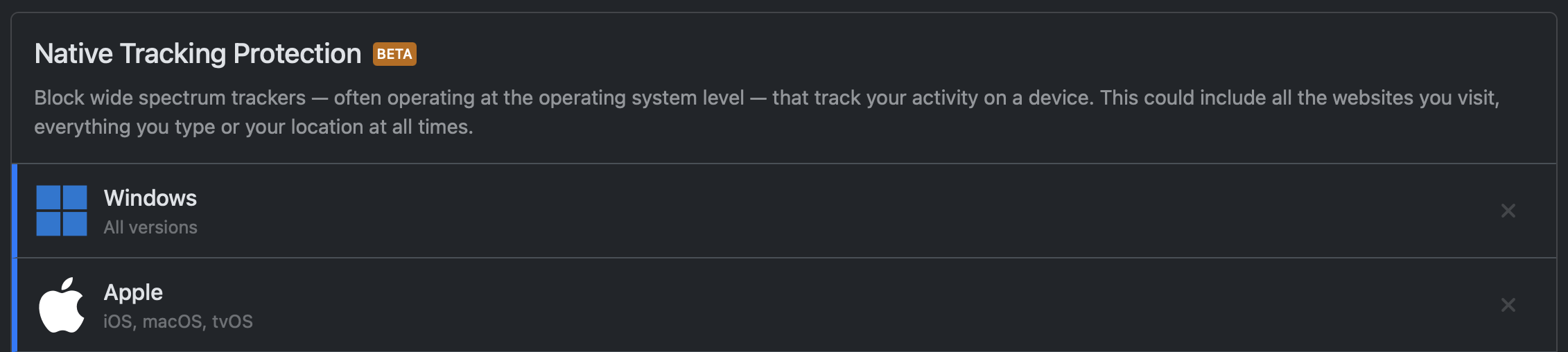
Or how about block platform-specific tracking and ad's without including a list that breaks other things like Snapchat and Instagram? Yep, just a toggle.
Traditionally, eliciting similar functionality from alternates has either been not possible (because it's not a customizable service) or very poorly implemented.
NextDNS also provides advantages in other areas. In this blog I'll aim to cover NextDNS's advantages in
Resolution Protocol Matters!
The more traditional solutions like Quad 9 (9.9.9.9) and PiHole still rely on unencrypted DNS. For the longest time PiHole and Quad 9 didn't offer any encrypted DNS solutions for resolving queries such as DoT and DoH.
These protocols add a few layers to DNS that provide privacy and security. For our use cases, namely avoiding digital censorship, maintaining privacy in airports, lounges, etc. this feature set is paramount. WiFi in public locations is now mostly ran by for-profit WiFi providers on contract for the large establishment you're visiting. WiFi providers routinely collect and sell data captured on their networks for tracking and advertising purposes. This information can even be sold to governments to allow tracking civilians en-mass 1.
There Are Flaws with PiHole..
The privacy and security capabilities able to be achieved with PiHole are significantly limited. This is primarily due to PiHole's deployment options. With PiHole you are practically limited to two main deployment methods:
Expose PiHole's port 53, 443, or 853 on your home network to the world.
Use a VPN back home that you forcibly tunnel DNS through to your home PiHole.
Both of these methods are easily identifiable by a local network that you're accessing your PiHole from. This is due to the use of a highly unique IP address, the public v4 address associated with you by your ISP. Because of this address distinctiveness, it allows for your network traffic to make you very trackable as you move between public access network locations.
The mentioned deployment topologies for PiHole also have the downside of needing to be regularly disabled in order to login to captive portals, or in the case of using plain UDP53 DNS, DNS responses may be transparently rewritten by the provider network infrastructure or malicious users. These deployment topologies for PiHole also have the negative of significantly increasing experienced internet latency on web pages because of the added latency this topology adds to query resolution.
There are counterpoints and claims that NextDNS doesn't really move the bar that much over PiHole. Those counterpoints do hold some value and truth provided the comparison is being done between like configurations. In this case we'll compare NextDNS DoH with what the actual and potential DoH implementations for PiHole are.
Regardless of the chosen protocol to resolve DNS, the fact remains that NextDNS uses IPv4 anycast addresses to host resolvers. This is easily identifiable in public access network environments. However, the fingerprint-able nature of this is significantly reduced compared to the PiHole alternative of using a hyper unique home public IPv4 address to send all queries to. Regardless of using DoH, DoT, classic UDP53, TLS SNI inspection, etc.
Using NextDNS with DoH (compared to the best case PiHole DoH alternative) shifts the trackable surface from "Dude in the airport that's sending a lot of traffic to a home IP address in Ohio" to "Dude in the airport that's using NextDNS to resolve DNS". Through this analogy we can see that the NextDNS DoH solution does indeed make you trackable in the worst case because your device is accessing a unique public resolver, or group-able in the best case because other people and services may be using NextDNS anycast addresses 2. Notably, NextDNSs solution does not make you identifiable as the PiHole alternative does.
Platform Integrations
NextDNS absolutely curb stomps the competition here. For this case example, I'll be looking at Apple devices as they are standardized and show the biggest wins in this department due to their design principles.
Apple has designed their software to try and be smart for the user. They're not exactly wrong to do this as most users genuinely don't know what is best for them in terms of security. However, Apples design decisions can be relied upon to attempt to solve issues for users that users may be trying to solve for themselves. This means that for technical implementors like yours truly, technical implementors sometimes or frequently loose the ability to control how Apple's software performs various actions.
Integrating a solution like PiHole into an Apple device usually results in very little success. The core platform (like Safari) and general apps can bypass DNS settings on iOS 3 4. This fact means that despite your best intention, the Apple device is likely to regularly be in situations where it simply ignores your preferences. This is useful in the case of captive portals!
However, once we're authenticated and authorized to use the network, our goal then shifts back towards reducing all the data we can that trackers, advertisers, data resellers, etc. can gather about us.
The solution NextDNS chose to go with for Apple devices is quite elegant. Many large corporations issue Mac's to employees. In support of this business practice, Apple came up with mechanisms to allow for "fleet management" of large scale Apple device deployments for security and compliance with corporate policies. This is Apple's MDM services and capabilities. NextDNS's solution to privacy configurations on Apple devices being optionally bypassed by applications, etc. is to use the business-need solution, MDM, that gives technical implementers at corporations the control to do exactly what we are trying to do.
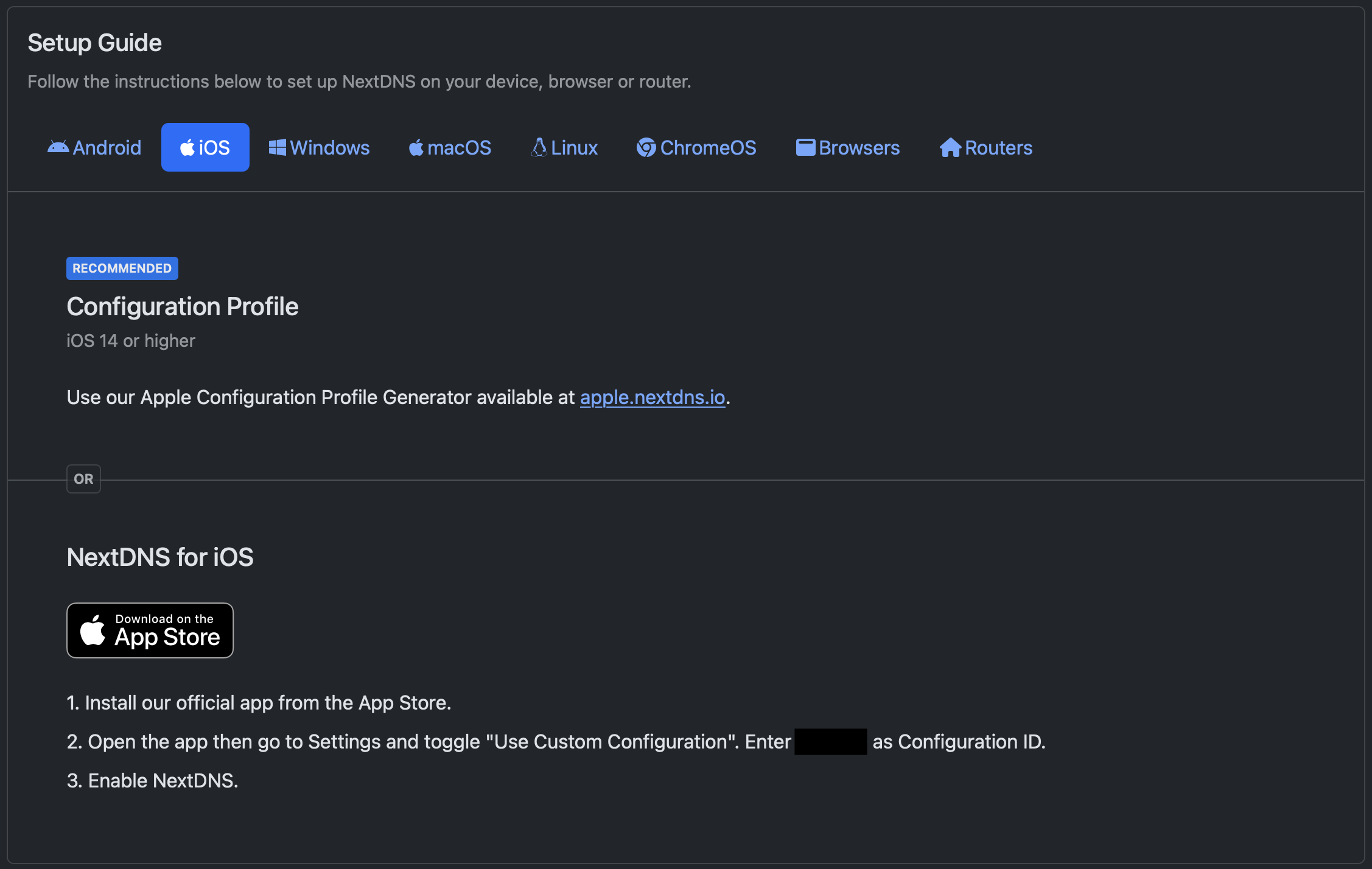
The NextDNS MDM config downloader is just over here! It's ease of usage is on-brand for NextDNS:
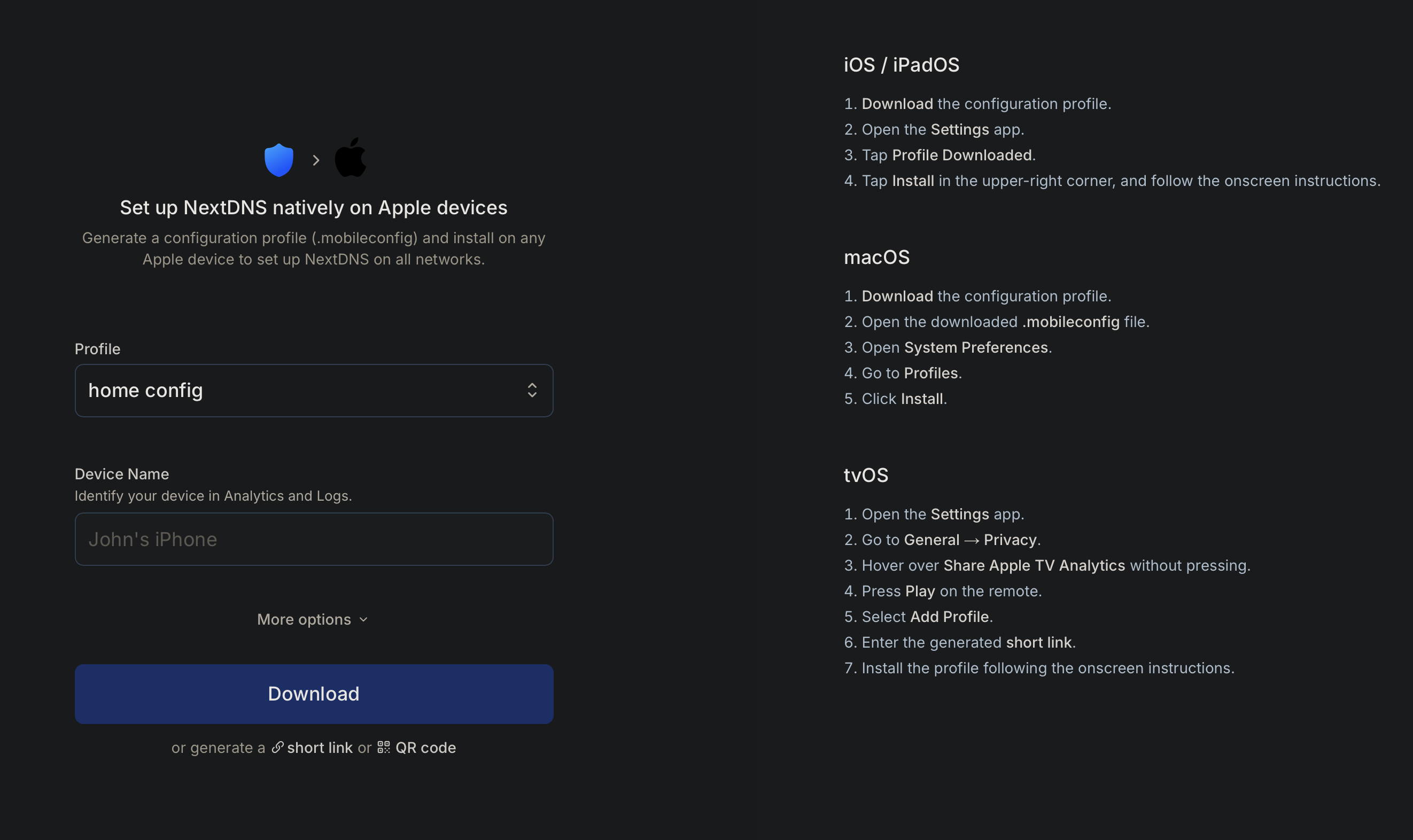
In general, the best experience with NextDNS is to be had when using the recommended configuration mechanism. For Apple devices that's MDM. When using the alternates, you're much more likely and even probable to experience friction in my experience.
The configuration options are quite thorough including supporting a variety of routers directly.
You can find the full list of supported linux and router platforms here
Failures of NextDNS
I have to talk about the state of Android secure DNS. It's pathetic and unfortunately even NextDNS can't really fix it. Android has no native solution to use DoH. It only supports DoT. This makes secure DNS on Android highly fingerprint-able and easily block-able on corporate and tracking-hungry networks. I feel compelled to count this as a NextDNS failure because the alternatives that NextDNS offers don't really work without user friction. Which is certainly one of my requirements for NextDNS.
As a result. I've found that the best method currently is to utilize TailScale on Android devices. This is a whole can of worms for a different time, but TailScale allows you to configure the upstream resolver in the TailScale administrative interface.
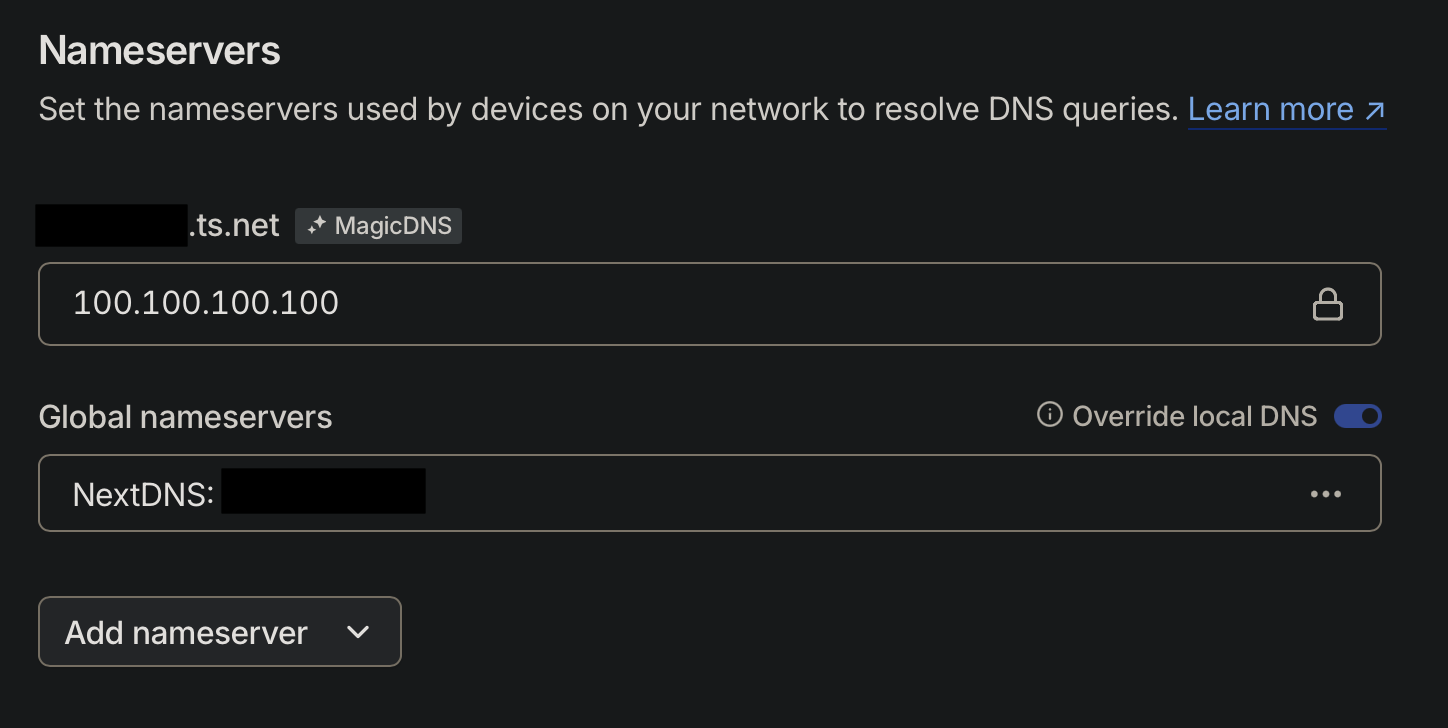
Through my testing, this has led to a very stable DoH implementation for Android devices.
I used the NextDNS test site, https://test.nextdns.io, to test: